This is what happens when my brain calls in sick due to burn out. I start actually playing with my toys…
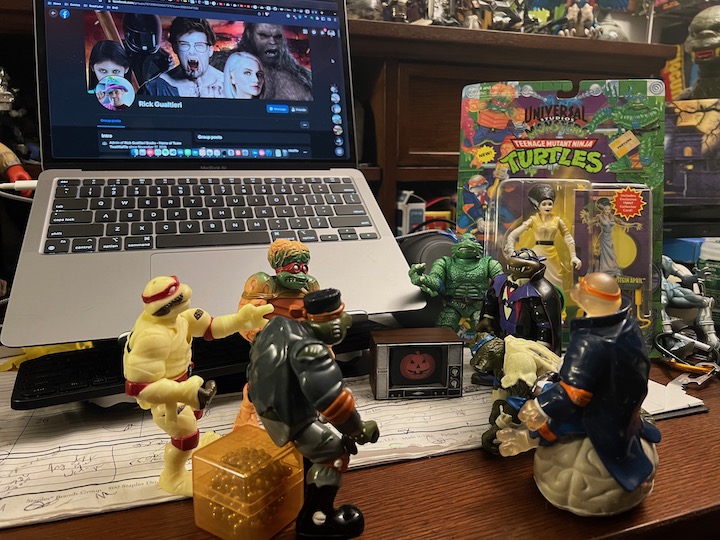



Video commentary on what happens when my brain burns out… 😛
Well for now at any rate. Considering a move to Jekyll or Hugo. Or at least a new server…
In the mean time, here’s a cat photo.

Hostapd with TN822N (RTL8192cu chipset)
http://forum.odroid.com/viewtopic.php?f=17&t=3028&start=20#p41229
https://github.com/pvaret/rtl8192cu-fixes/blob/master/README.md
http://askubuntu.com/questions/401045/wifi-problems-with-tp-link-wn822n-ubuntu-13-10
Do the following (from the github/pvaret link):
sudo apt-get install linux-headers-generic build-essential dkms
git clone https://github.com/pvaret/rtl8192cu-fixes.git
sudo dkms add ./rtl8192cu-fixes
sudo depmod -a
sudo cp ./rtl8192cu-fixes/blacklist-native-rtl8192.conf /etc/modprobe.d/
then fix / replace the hostapd binary:
1. Download this -> http://www.realtek.com.tw/downloads/downloadsView.aspx?Langid=1&PNid=48&PFid=48&Level=5&Conn=4&DownTypeID=3&GetDown=false&Downloads=true#RTL8192CU (the file is called RTL8188C_8192C_USB_linux_v4.0.2_9000.20130911.zip)
2. Make sure you are running the latest kernel.
3. Unzip that new zip file you download
Go to: RTL8188C_8192C_USB_linux_v4.0.2_9000.20130911/wpa_supplicant_hostapd
4. unpack the hostapd tarball:
tar -zxvf wpa_supplicant_hostapd-0.8_rtw_r7475.20130812.tar.gz
Go to this folder: wpa_supplicant_hostapd-0.8_rtw_r7475.20130812/hostapd
5. Run: make -j5
Install it: cp hostapd /usr/sbin/hostapd_realtek
modify /etc/init.d/hostapd:
DAEMON_SBIN=/usr/sbin/hostapd_realtek
/etc/hostapd.conf
# Define interface
# Select driver
#wlan1 realtek
#driver=r8169
#wlan0 asus/atheros
#driver=ath9k
#wlan0 asus/atheros
# Set access point name
# Set access point harware mode to 802.11g
# Set WIFI channel (can be easily changed)
# Enable WPA2 only (1 for WPA, 2 for WPA2, 3 for WPA + WPA2)
interface=wlan1
auth_algs=3
logger_stdout=-1
logger_stdout_level=2
max_num_sta=5
bridge=br0
channel=5
country_code=US
#driver=nl80211
driver=rtl871xdrv
#dtim_period=1
fragm_threshold=2346
hw_mode=g
ieee80211n=1
rsn_pairwise=CCMP
rts_threshold=2347
#ssid=hp48sx
ssid=test-ssid
wmm_enabled=1
wpa=2
wpa_key_mgmt=WPA-PSK
#wpa_pairwise=TKIP
wpa_pairwise=TKIP CCMP
wpa_passphrase=my-passwd
#ignore_broadcast_ssid=1
macaddr_acl=0
My big accomplishment for the day was getting Linux authentication working through an Active Directory one-way transitive trust with winbind and kerberos…
Yeah, nobody at work had any idea what I was talking about either. They just heard my maniacal laugh as I ran out of the building…
http://www.theregister.co.uk/2014/10/17/cloud_migration/
https://github.com/nabla-c0d3/sslyze
http://www.theregister.co.uk/2014/10/16/windows_containers_deep_dive/
https://www.poodletest.com/
Found at https://code.google.com/p/chromium/issues/detail?id=410805 ## download stable to /tmp/chrome mkdir -p /tmp/chrome cd /tmp/chrome wget http://mirror.pcbeta.com/google/chrome/deb/pool/main/g/google-chrome-stable/google-chrome-stable_37.0.2062.94-1_amd64.deb ## split out the archive ar vx google-chrome-stable_37.0.2062.94-1_amd64.deb ## extract data tar --lzma -xvf data.tar.lzma ## copy libpepflashplayer.so & manifest.json to /opt/chrome cp opt/google/chrome/PepperFlash/* /opt/google/chrome/PepperFlash/ # open chrome and test... You may want to keep a copy of libpepflashplayer.so & manifest.json around to replace upgraded versions with until this is fixed. Be sure that you enable click-to-play to help prevent malicious flash programs.
Recent Comments